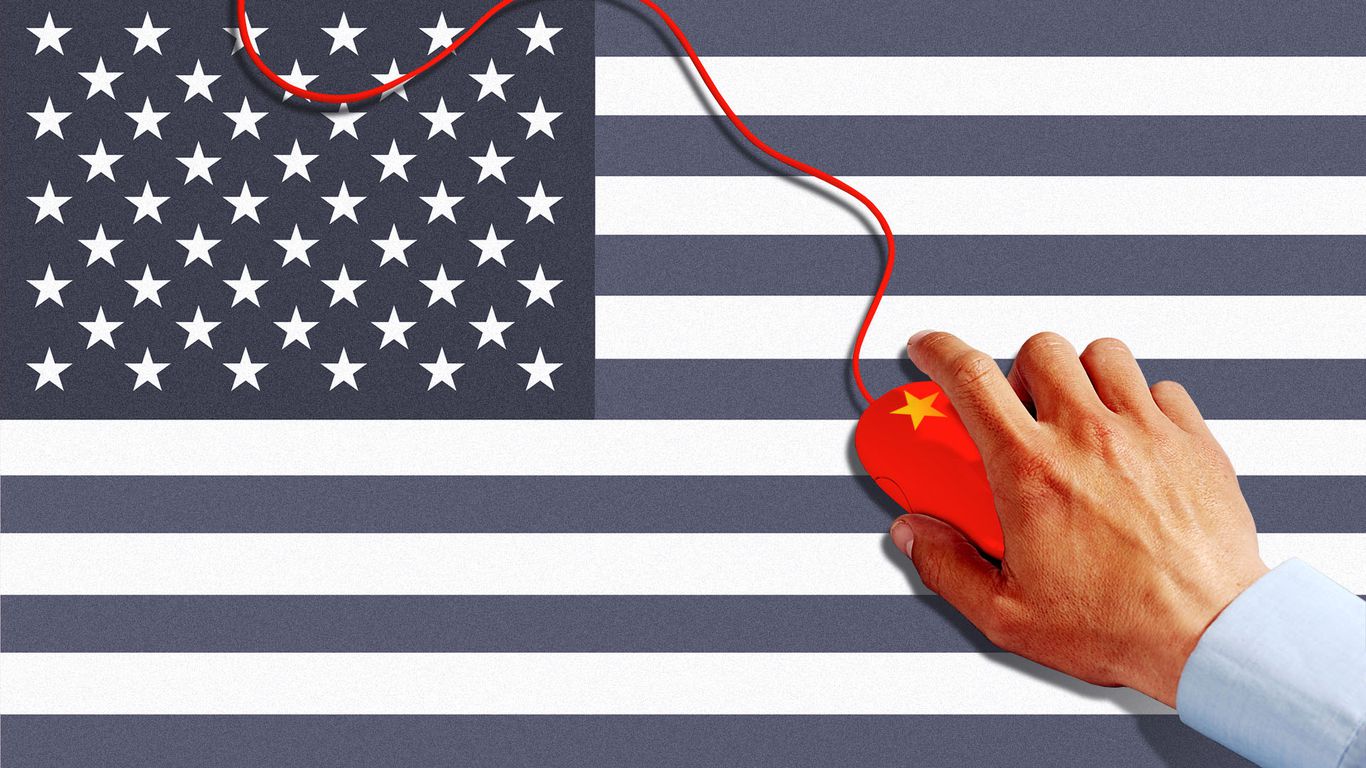
Exclusive: Suspected Chinese hackers impersonate U.S. briefings in phishing lure
Summary
A suspected group of hackers based in China created a phishing campaign that pretended to be U.S. policy briefings to target diplomats. The phishing attack successfully infected many people and was discovered by a cybersecurity firm named Dream Security. This campaign involved sending fake official documents via email, which, when opened, allowed hackers to access the devices.Key Facts
- A China-based hacking group launched a phishing attack around Christmas.
- The cyberattack pretended to be U.S. policy briefings.
- The attack targeted diplomats and officials involved in global affairs.
- Fake emails sent between December and January contained harmful attachments.
- Simply opening the fake document compromised the device.
- The hacker group Mustang Panda is believed to be behind the attack.
- Dream Security, an Israeli firm, discovered the campaign.
- Dream's AI agent was the first to uncover such a China-linked attack.
Read the Full Article
This is a fact-based summary from The Actual News. Click below to read the complete story directly from the original source.